What is an Access Control System and How Does It Work?
An Access Control System is essential in modern security. It manages who can enter specific areas or access particular information. These systems use various methods, such as keycards, biometrics, or PIN codes. Each technology has its strengths and weaknesses.
Understanding how an Access Control System functions is crucial for businesses and organizations. They help protect sensitive data and valuable assets. Yet, they are not foolproof. Systems can fail or be bypassed if not properly managed.
Designing an effective Access Control System requires careful planning. It involves assessing different risks and choosing the right technology. The implementation process can be complex and often needs regular updates. Reflecting on these aspects can lead to better security solutions.

Definition of Access Control Systems
Access control systems are critical for safeguarding physical and digital assets. These systems determine who can enter specific areas or access data. By defining permissions, they help organizations manage security effectively. A well-structured access control system can greatly reduce unauthorized access incidents. According to a recent industry report, over 70% of organizations have faced breaches linked to inadequate access controls.
Access control systems typically include components like identification, authentication, and authorization. Identification verifies who you are, while authentication confirms your identity. Authorization then defines what you can access once verified. Each step is essential in creating a robust security framework. Surprisingly, about 60% of companies do not regularly review their access control policies. This oversight can lead to vulnerabilities.
**Tips:** Regular audits can identify gaps in access control. Simple checks, like updating password policies, can enhance security. Ensure employees receive training on access protocols. It’s crucial to stress that even the most sophisticated systems depend on human oversight. Neglecting to engage staff can render any system ineffective. Remember, an access control system is only as strong as its weakest link.
Access Control Systems Usage Statistics
This chart illustrates the distribution of different types of access control systems used in various environments. The majority of organizations favor physical access control, while role-based and mandatory access controls are less common.
Key Components of Access Control Systems
Access control systems are vital for safeguarding physical and digital spaces. These systems consist of several key components that work together to ensure security. One primary element is the access control panel. This device manages permissions and tracks who enters or exits. It serves as the brain of the operation, coordinating all actions.
Next, we have the entry devices. These can include keycards, biometric scanners, or PIN code pads. Each method has its advantages and challenges. For instance, keycards can be lost or forgotten, while biometric systems raise privacy concerns. The balance between convenience and security is often a point of contention.
Finally, monitoring software plays a crucial role. It records data and generates reports on access activities. However, extensive data collection may lead to security risks if not adequately protected. Each component interacts, creating a complex network aimed at enhancing security. Yet, the effectiveness of an access control system often hinges on how well these elements function together. Regular updates and assessments are necessary to address vulnerabilities and improve overall performance.
Types of Access Control Mechanisms
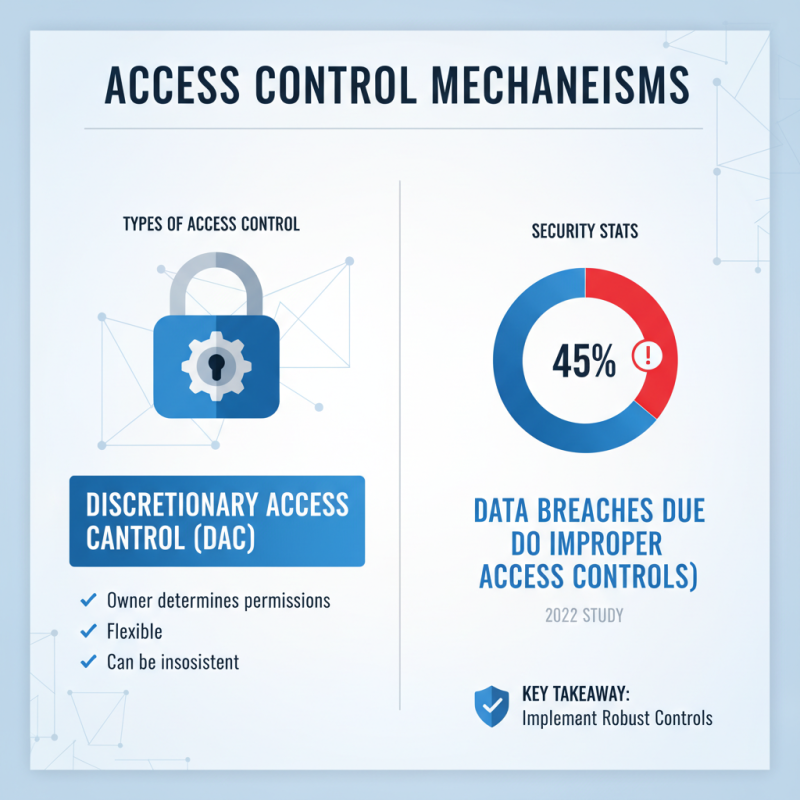
Access control mechanisms are essential tools for managing who can access specific resources. They can be categorized into several types. One of the most common types is discretionary access control (DAC). In DAC, resource owners determine access permissions. This method allows flexibility but can lead to inconsistent permissions. A 2022 study found that 45% of data breaches occur due to improper access controls.
Another influential type is mandatory access control (MAC). In MAC, access permissions are determined by a central authority based on information classification. This model is often used in high-security environments. While it enhances security by enforcing restrictions, it can be rigid and challenging to manage. A report indicated that organizations using MAC systems experienced 30% fewer security incidents.
Role-based access control (RBAC) is gaining popularity as well. This method assigns permissions based on user roles within an organization. It simplifies management but may not adapt quickly to organizational changes. A 2023 survey revealed that 55% of businesses using RBAC struggled with outdated roles. Access control mechanisms are crucial yet require constant evaluation to remain effective.
How Access Control Systems are Implemented

Access control systems are essential for securing physical spaces and digital resources. These systems rely on various technologies to manage who can access specific areas or information. Implementing an access control system starts with identifying the needs of an organization. Each space may have different security requirements. For example, a server room has higher access restrictions than an employee lounge.
Next, determining the type of access control is crucial. Systems can be keycard-based, biometric, or mobile-based. The choice may depend on the level of security needed and the budget available. Many organizations face challenges here. Employees may misplace keycards. Biometric systems can sometimes fail. These pitfalls require planning and occasional adjustments to ensure functionality.
After determining the technology, setting up the infrastructure is vital. This includes installing hardware like locks, cameras, and control panels. Integration with existing systems can be tough. Training staff is another key factor. Without proper understanding, even the best systems can falter. Regular audits help identify gaps in security protocols. A well-implemented access control system is an ongoing process, not a one-time fix.
Benefits and Challenges of Access Control Systems
Access control systems offer significant benefits in securing physical and digital assets. One of the most compelling statistics is that organizations with access control systems can reduce security breaches by up to 30%. This reduction stems from enhanced monitoring and restricted access capabilities.
However, implementing such systems is not without challenges. Many companies face resistance from employees who may see these measures as intrusive. This hesitation can lead to gaps in compliance and effectiveness.
Another noteworthy benefit is the scalability of modern access control systems. Data from industry reports suggest that 70% of organizations using advanced systems can easily adapt to changing security needs. Yet many systems struggle with integration. Companies often find it difficult to merge new technologies with existing infrastructure. This can lead to inefficiencies and frustrations among users.
Moreover, while access control systems provide valuable data for tracking attendance and movements, they can also raise privacy concerns. A survey revealed that 40% of employees feel uncomfortable with constant monitoring. Balancing security and privacy is a persistent dilemma. Organizations must navigate these complexities carefully to ensure that their security measures do not compromise employee trust.
Related Posts
-

Why is Access Control System Essential for Security?
-

5 Digital Strategies to Optimize Your Best Access Control System Purchase
-

Digital Strategies to Enhance Your Access Control Security with Proven Data Insights
-

Unlocking the Future of Access Control Security with Digital Solutions
-

How to Implement Effective Access Control for Your Organization's Security
-

Choosing the Right Manufacturer for the Best Biometric Machine to Ensure High Quality and Reliability